Ali Allage is back with The Trusted Advisor. In this episode Charlie and Ali focus on how the remote work landscape has affected the cyber security health of many companies. We also review what questions an insurance agency should be asking potential customers when selling them a cyber liability policy.
Edwin K. Morris (6s):
Welcome to the trusted adviser podcast brought to you by Iroquois. Iroquois is your trusted advisor in all things insurance. This week, you are listening to the special segment of Charlie’s corner hosted by our very own Charlie Venus.
Charlie Venus (22s):
Welcome back to our guest, Ali Allage, CEO of blue steel cyber security. We are continuing our conversation from last week on how working remotely has changed the landscape of cybersecurity. How has remote work changed the landscape of cyber security?
Ali Allage (40s):
A lot of, what I’ve seen, a lot of organizations who have difficulty ensuring that policies and procedures are being followed. What we’re seeing is that the end-user is installing more devices and are running into challenges. Because quite frankly, in a lot of, of these organizations had to quickly switch to a remote work environment and weren’t necessarily prepared to do so. And with that comes a lot of rules being created on the fly. And so when you have rules of being created on the fly, you have these gaps and during those gaps, you have users that are sort of installing applications that normally wouldn’t install if they were in the office, that are opening up security compromises and, and vulnerabilities.
Ali Allage (1m 23s):
There’s been a lot of efforts in a, in a sense of assessment and doing a scan in vulnerability tests on the end-user devices and seeing what sort of operations are being conducted on the end-user devices. And then reigning it back in to some sort of a controlled environment, managed environment. Security professionals, we all wanna have managed environments ’cause then we know what’s been added, what’s being removed. And when we went to remote, that’s sort of when we went into a wild, wild west and that managed feeling has gone away. And so we’re, everyone is trying to bring it back to manage. So
Charlie Venus (1m 57s):
When you look at a policy for remote workers, with some of those things being just that it’s all company issued equipment that the workers are using, not their own personal equipment. Yeah.
Ali Allage (2m 10s):
We have some customers who have had policies for a full reimbursement for technology purchases rights. So if you join the company and you wanted to buy, let’s say the Mac book, you got the full reimbursement for that. That’s even, you know, in the case with mobile devices, mobile devices are probably one of the hardest devices to rein in, as far as management is concerned. For security management, what the position is, it’s sort of, of the competitive landscape for keeping great personnel in and hiring or attracting new talent. There’s a compromise that’s being made in the sense that if we want a users to be happy with the technologies that they bring to the table, right? Not everyone is a PC user.
Ali Allage (2m 51s):
For example, I prefer a Mac book, not everyone has a Mac book and they prefer PC usage. And a lot of times there is the overlap in personal usage amongst a business. Some of the tools sets that are out there that are available to security professionals allow for management of individual devices while still keeping it somewhat secure. So it may not be something where they’re able to do whatever it is they want, but it keeps it in a place where there is a happy medium. And I think without the tools and then the match of the policies, I think this would’ve been really difficult. So if I think about in terms of a couple years ago, this was probably not possible. And I remember those days because everyone, when we were talking about work at home policies for like one day a week, it was about how do I measure productivity of my end user?
Ali Allage (3m 35s):
Or how do I know whether or not they’re doing work when they’re not in the office? And so I think it sort of evolved from that mindset of like, well, forget about that so much. How do I make sure that the end-user is happy and it’s able to use the device in some ways in the way they want, but while we are still being able to manage our security practices. It all comes down to some of these tools sets that are available and I think that’s made it a lot easier to manage.
Charlie Venus (3m 58s):
What’s the cost to firm’s if they don’t have a cybersecurity program? And does size really matter when it comes to having the cybersecurity program?
Ali Allage (4m 7s):
Well, what’s the cost to the organization. It’s hard to measure. And the reason why I say that, because you can see ransoms that are out there, right. A 5 million, 1 million, 500,000, whatever. Right? And so that’s a measurable cost of whatever you, you pay or don’t pay in ransom that has its own Metro costs. I think the part that’s sort of difficult to sort of measure is the impact, right? So if you have a breach, chances are, it’s going to be known somehow if you’re focused on presenting a posture of saying that, you know, of working with us, building trust with your, the organization and customers, security is a major component of that. I look at it as a marketing component, a very valuable marketing component. And if that’s violated in any way, it’s difficult to sort of come back from that, right?
Ali Allage (4m 52s):
We’ve seen major organizations that have had breaches had to go through a rebrand because ultimately the, the, the age of the brand doesn’t matter anymore if you had a breach. Right? So I would say it’s significant in terms of the cost of depending on the size of the organization. We as vendors look at it in terms of a per user cost, right? So there is a cost associated in terms of management of every individual user in the organization. So if you’re a 50 person user base, right, it’s gonna be a different cost than if say you had 250, just because of that quantity of users. But I think as you scale the organization to 500,000, several thousand, the impact of all those moving parts and how much data acquisition is occurring, who has access to what data, forgetting the fact that if you’re being breached and you have a disgruntled a staff member?
Ali Allage (5m 43s):
The exposure is such a high, high cost. It’s unbelievable. I typically say as a vendor, outside of having a cybersecurity risk policy in place, we as the vendors are a, an additional supplement to that insurance policy. We ensure that you meet the requirements and compliance of that policy is one, but two, we help the reputation of the organization by minimizing and showing that there’s active pursuit of maintaining a cybersecurity maturity that prevents most of these common breaches that are occuring out there.
Charlie Venus (6m 17s):
But when you look at the breaches that are occurring, and if a company does have a cybersecurity program in place, what percentage of these breaches would be eliminated or prevented?
Ali Allage (6m 28s):
There was an interesting statistic out there. Most of the breaches that are occurring, a majority of them are what we call a, I guess, kiddy programmers, right? So what that means are these are inexperienced developers, technologists that are picking up pieces of frameworks that are out there floating for what we call frameworks out there for them to adopt. Using that model that was mentioned about sending a phishing email to a thousand users or a 5,000 users, the majority of the attacks that occur and get exploited are from those initial efforts. So these are statistically younger people that have very little experience using standardized or like off the shelf, packing techniques and penetrating these major organizations.
Ali Allage (7m 11s):
And so when you asked me the question if a company has a basic level of cybersecurity hygiene, what’s the percentage of prevention – it’s significant. And I don’t know, I might be crucified for saying this because a lotta times you see a security promotion saying, if you adopt this practice, you won’t get penetrated and a, a a a hundred percent safe. Statistically, not true. You are just trying to prevent 90 to 95% of what’s occurring out there and not becoming a statistic. Whereas the 5% that’s occurring, those are a, a such a high level of sophistication that if you’ve been targeted, your security program has to go to a whole different level because you have someone who is actively pursuing you that is highly experienced.
Ali Allage (7m 52s):
But the majority of these cases, most of them, 90% of them are based on inexperienced individuals that are just trying to gain access because a basic control wasn’t met.
Charlie Venus (8m 2s):
What types of assessments are there for the cybersecurity programs that are in place?
Ali Allage (8m 7s):
It depends. Everyone has their purchase. I look at it in the sense of compliance. So NIST has great standard’s to follow, in there’s 800-171. There are different other international standards like ISO 27,001. The approach we take is that we look in terms of NIST 800-171 as a base line. It’s about 110 controls. It sort of covers a wide range of different variables. There’s a scan and vulnerability side to the systems. There’s a risk assessment interview, a that’s done across the organization. So we try to look at the human side and capture that. We look at the technical side and then I think what’s really important is, once you identify vulnerabilities or as you’re scanning the systems, is to pick and choose some approaches, what we call threat modeling and attack.
Ali Allage (8m 55s):
And so we exploit vulnerabilities that exist and see, could we obtain access to certain pieces of information? I think, you know, red flagging and you know that this could be an issue that could be an issue is one thing. But I think also showing that the fact that we used that in order to gain certain access privileges is really, it hits home. I think every time we do these assessments, right, we, we talk about the risk assessment in interview. You sorta get a glazed over look. We say, look, here’s your vulnerability scans that we’ve done and show you all of these things that are prioritized from critical, high and areas that you have to address. You know, I know from an executive level, both of these are like, oh my gosh, how much is this going to cost me to sort of put this together?
Ali Allage (9m 35s):
But when we show that we took one of these items, right? And we ran a threat model and we gain exposure to XYZ pieces of information, it changes everything. Because when you can say that you can use it towards an advantage as an outsider coming in, it sort of hits home. So that’s how we conduct our assessments. We want to really tie it back in and show you that this could really happen. You should address the certain areas of gaps.
Charlie Venus (10m 5s):
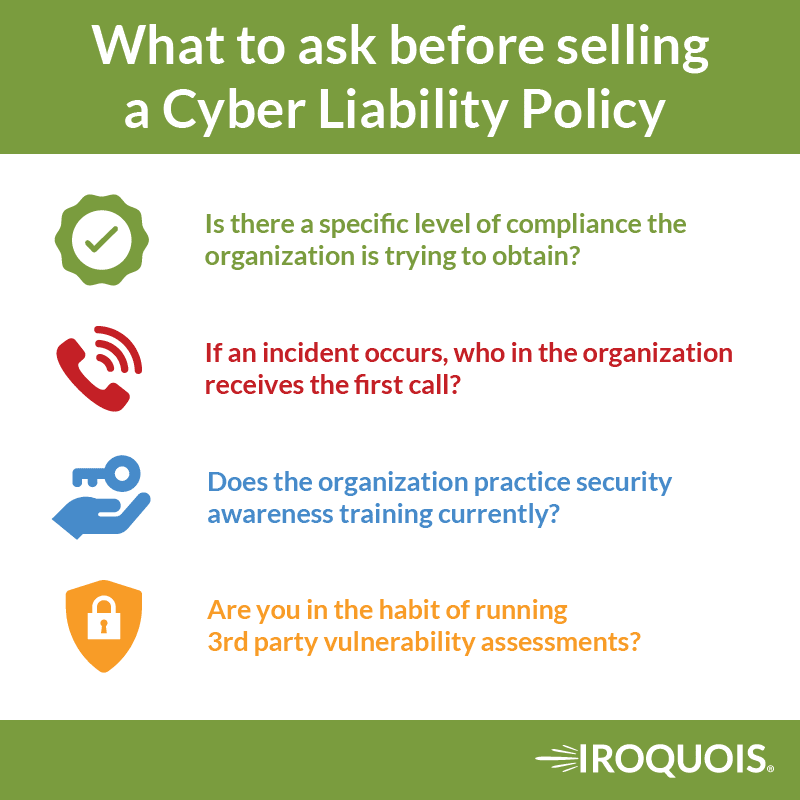
We have member’s out there that, as I said earlier, that are out there selling the cyber liability policies to protect their clients against the cyber losses. When they’re going out there to meet with their clients and they’re trying to do an assessment in simple terms, what would be the focus of the three or five questions that they would be asking their clients about what their current cybersecurity controls are?
Ali Allage (10m 33s):
Being the compliance person, I would ask, is there a specific compliance that the organization is striving for or is looking to take, a security compliance or some form of it. Going through HIPPA compliance or, is just, there are a security controls. They’re as an example, if they were going through an ISO certification or are going through those kinds of compliance measures, to ask them, what is the approach? They’re, the second thing would be if there was a security incident, who gets called on first, who is a reporting person, a frontline person in the case of a security incident happening. I usually like to ask that question, cause sometimes the person that you are asking is fumbling with it. And if you see a fumble, chances are that is not even thought out, which would be a red flag or concern.
Ali Allage (11m 14s):
And then I would ask the question, and I think I mentioned this early on, is out of the entire organization, do you guys practice security awareness training and is the staff it up to speed, as far as your security practices and sort of get an answer there. And my followup question would be, can I randomly choose someone in the office and just ask them about the policy, you know, right after this meeting. And so see if their eyes light up or something like that occurs, right? Because then that will help them validate whether or not something needs to happen. And then ask them periodically how many times out of the year do you do a third-party independent vulnerability assessment or a security assessment, or do you do third-party audits? I like that question.
Ali Allage (11m 54s):
Because the compliance measures that are coming into place and that are sort of evolving are all moving towards third-party evaluation. And so asking them do they do a third party evaluation and who that third party is. That will help kind of give another guidance. And I think those are good, great basic questions. The idea of trying to really gauge to see if they have a security practices in place, that one that they didn’t just grab off the shelf, but two to see if they’re in practice. I think those are two distinct areas. Anyone can go grab templates, anyone can go to source those pieces of information because they’re out there and they are freely available. I think the tough part for a lot of organizations is whether or not they put into practice. Cause that takes organizational effort, that takes a sort of executives promoting it and distributing it amongst the entire staff.
Ali Allage (12m 40s):
I try to look for those two areas and see where they are. As far as maturity level,
Charlie Venus (12m 44s):
And when you get to the remote workforce, would you be asking, can I contact somebody or a couple of people remotely to see how they respond?
Ali Allage (12m 51s):
Oh yeah. I would highly suggest a phone call or zoom call. A video call would be the best, a phone call will be second tier, and then the rest we may have to do via email but email has too many, too many gaps. People could search for answers or we’re not provided. The video part, well, again, I just mentioned the white in their eyes. You wanna see that, you want to see the surprised look to kinda give you all of the information you need right there
Charlie Venus (13m 16s):
What about multi-factor authentication? And just briefly there, we have some of our carriers that write cyber liability coverage. They are now requiring multi-factor authentication to even offer the coverage now, which is relatively new, just in the last couple months.
Ali Allage (13m 34s):
All of these pieces are very great starting points and they should be employed. Cybersecurity is not a task. It’s a program. I’m a big fan of identifying what your focus of your program is. And then adding these puzzle pieces to compliment that program, to supplement that program. When it comes to multifactor, I think it should be enabled across the board hands down. But I think there should be a little layer of detail in to that how that’s enabled because in certain cases, even with multifactor, some of the stage gates can still be penetrated. One example would be a lot of the organizations use multi-factor out there where it sends an email confirmation code or it sends a text message. But those are two areas of compromise still. Where some of the areas that I would recommend is looking at like Google authenticator or Microsoft authenticator some of these authenticator apps where they generate the codes for you based on a scan those are probably the best that when you enable multifactor, it maintains the program that keeps things pretty well secured.
Ali Allage (14m 31s):
Applications that are services that don’t offer multi-factor really comes down to making sure that you identify the end inventory or what it is and what isn’t multifactor capable and figuring out different solutions to make sure the ones that are not able to be enabled, to come up with different ways of trying to secure and lock down those accesses.
Charlie Venus (14m 50s):
Where do you see the cyber crime going? Do you see we’re getting control of that in any way, shape or form, or are you see a, just a ballooning even more?
Ali Allage (14m 58s):
There’s a couple of ways I could answer that. You know, I think in terms of a growing, when you say ballooning more, I, I see that growing exponentially. A reason why I say that is because it’s becoming a business model. And as we know with anything that has a, a real full fledged business model and it’s easily adoptable, especially when you’re using an I know crypto-currency, and that’s a whole separate conversation, but when you’re having a payment gateway systems are technically anonymous and then you have methods for people to sort of build startups in this environment. Then it becomes a situation where it, you know, everyone is going to jump in. When it comes to the fact that that being that, that market’s sort of exploding on its own.
Ali Allage (15m 41s):
I do think that the reduction of the statistical probability of being hacked or penetrated can be reduced. And I think it comes down to organizations really seriously thinking about the security as a program, but starting with the basics, we don’t need to make it complicated. We don’t need to go and sit there and say, we have to do a 130 control’s and invest hundreds of thousands and millions of dollars in order to really be truly secure. That’s not necessarily a case. As I mentioned before, a lot of times when companies get hit, it’s kind of getting hit by inexperienced hackers, developers. And so if you follow the basic principles and figure out how to consistently follow them, you’re a step ahead most organizations, but these attacks are going to happen, what’s gonna be interesting is how fast the market matures.
Ali Allage (16m 34s):
Entry level people coming into the hacker business model, basically they’re gonna start to learn more. They are going to get more experienced and the services and the tool sets the technology is just going to get more and more sophisticated and to get more, a more complicated to manage. But if you start now and you start getting your feet wet in this, as it gets complicated, your learning curve is not as steep. And I think that’s again, all about reducing the statistical odds and not a hundred percent prevention.
Charlie Venus (17m 1s):
Thanks, Ali. This has been a great conversation, a lot of great learning, in particular for me. Thanks again for joining
Ali Allage (17m 7s):
Awesome. Appreciate it. Thanks for the time. And that was really fun.
Edwin K. Morris (17m 11s):
Thanks for listening to this edition of Charlie’s corner brought to you by Iroquois Group. I am Edwin K. Morris, and I invite you to join us for the next edition of the trusted advisor podcast.